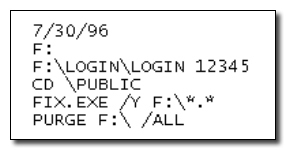
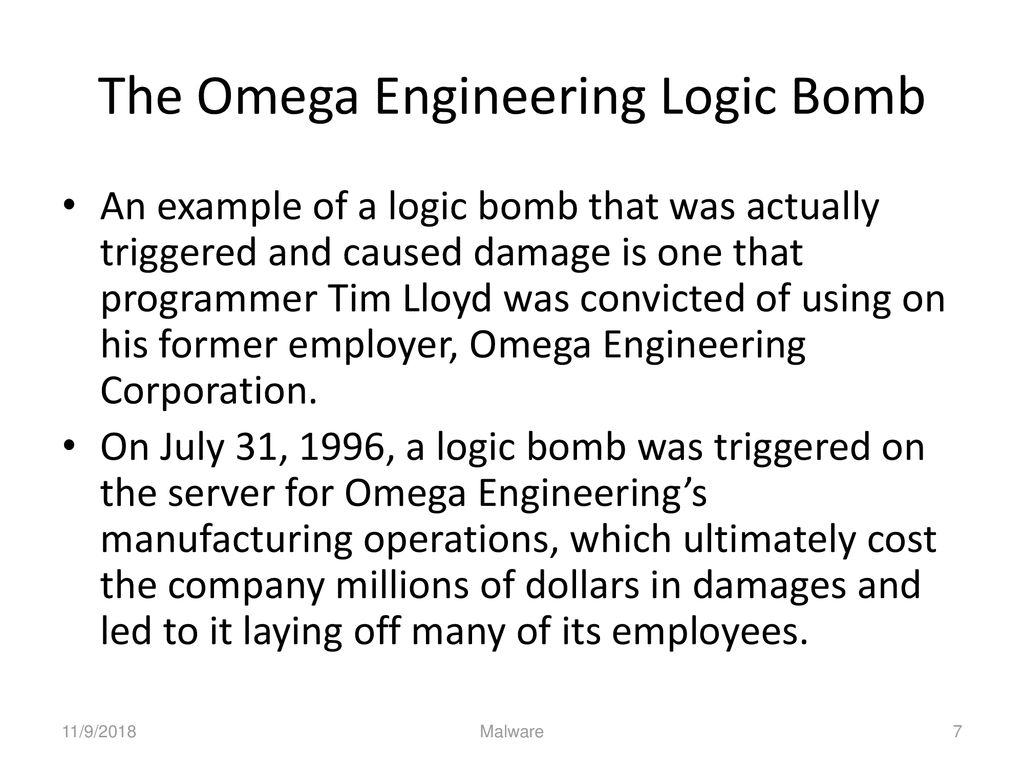
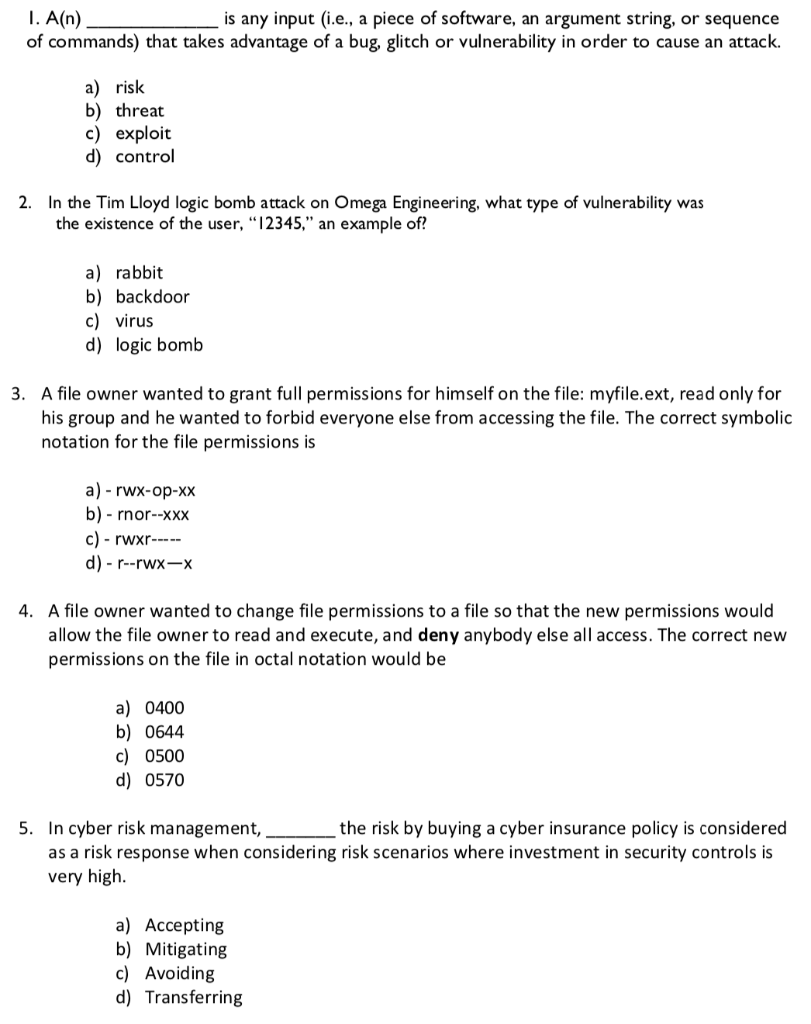
In the Tim Lloyd logic bomb attack on Omega Engineering, what type of vulnerability was the existence of the user "12345" an example of? | Homework.Study.com

Building a Solid Cybersecurity Foundation NACUSO Las Vegas April 4, 2016 PLATINUM PARTNER GOVERNANC E CYBER SECURITY POLICY FFIEC Risk Assessmen t RISK. - ppt download

IS4463 Secure Electronic Commerce 5:30-6:45 PM Robert Kaufman –Background –Contact information Syllabus and Class Schedule Student Background Information. - ppt download